6.4 Wireless Security on Linux
Once you have configured your wireless base station to use WEP
encryption the next step is configure the wireless network adaptor on
your Linux system to use the same encryption key so that it can decrypt
the data travelling over the network.
RedHat Linux provides a powerful graphical tool that makes it easy to
configure wireless security on your Linux system. On RedHat Linux
systems this tool is called:
redhat-config-network
On Fedora Core systems this tool is called:
system-config-network
The tool must be run with root privileges. If you are not root when you
run the tool it will ask you for the root password before letting you
proceed. The main screen of the configuration tool is shown in
Figure 6.4.
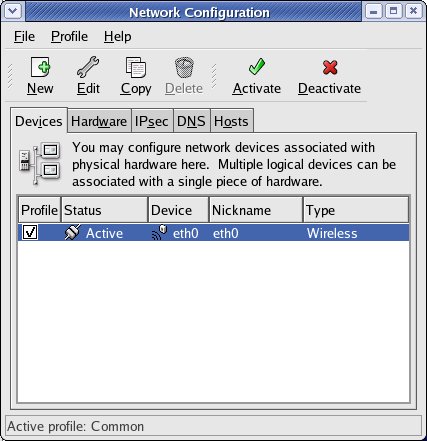 Figure 6.3 -
redhat-config-network Main Screen
Figure 6.3 -
redhat-config-network Main Screen
The main screen displays the active network devices on the system. In
the configuration shown there is one network device listed and this is
our
wireless network adaptor.
The next step is to configure the wireless encryption setting for this
device.
