It is refreshing in an industry filled with
cryptic terms
and three letter acronyms (better known as TLAs) to come across a name
that is
at least somewhat self explanatory.
Consider the internet to be
inferno of viruses, hackers and
cyber criminals all looking for systems that they can invade. Rather
like a
firewall in real life it stops any of this unpleasantness from
spreading into
your environment. Another good analogy is that of a fortress wall that
protects
the inhabitants that live inside. The firewall stops unwanted
connections from
entering your internal network much like the wall around a fortress
prevented
the marauding hoards in medieval times. Rather like the gate in the
fortress
wall the firewall allows only data and connections that meet certain
criteria
to pass through the wall to the internal network.
A typical firewall configuration
is shown in Figure 2.1. The
firewall is positioned between the outside internet connection coming
in
through the modem and the internal network on which reside a number of
Linux
and Windows systems. The firewall controls all data traffic and filters
out
anything that is not permitted to enter the internal network.
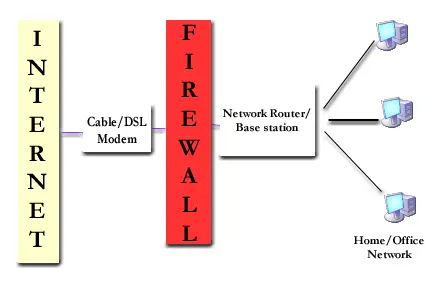
Figure 2.1 - A typical Firewall
Configuration
